Most security teams have one. Many have the other. Very few can explain clearly what each one actually does — or why the question of whether you need both has a different answer depending on who you ask.
Walk into most SOC conversations and you will hear both terms within the first ten minutes. SIEM and SOAR. Sometimes in the same sentence, sometimes as if they are interchangeable. They are not.
Understanding the difference is not just a vocabulary exercise. How you distinguish between them determines how you build your security operations, how you evaluate vendors, and — most practically — where the gaps in your detection and response capability actually are.
This post explains what each one does, where each one ends, and why the answer to ‘do we need both’ is almost always yes — but for reasons that are more specific than most explanations let on.
What SIEM Does — and What It Cannot Do
Security Information and Event Management. The name is almost self-explanatory, but the day-to-day reality of running one is less clean than the acronym suggests.
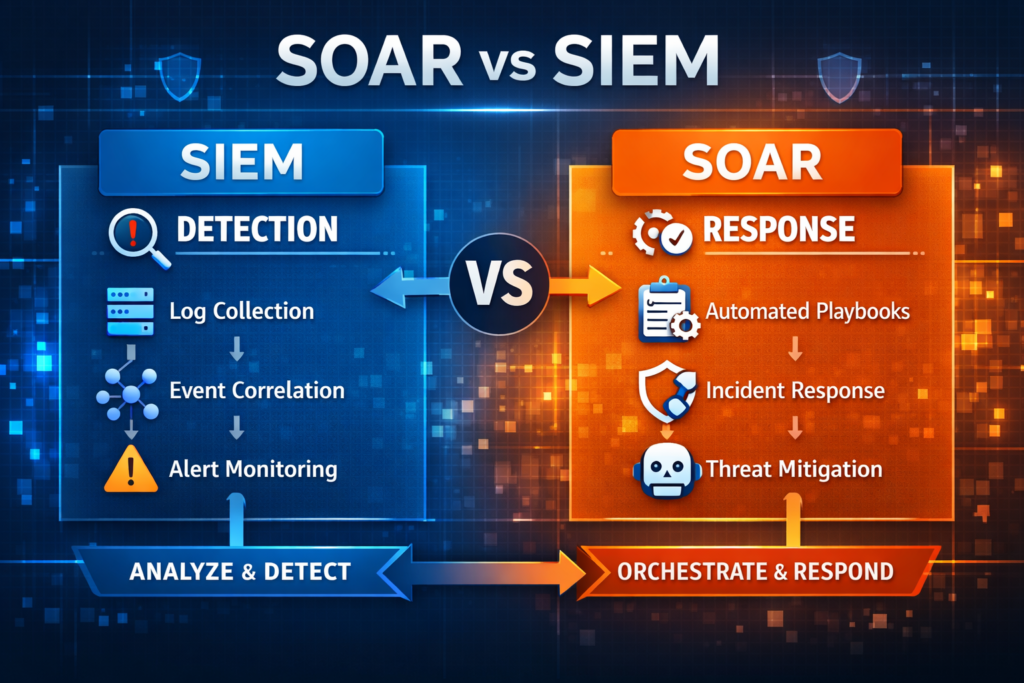
A SIEM collects log data. From firewalls, endpoints, servers, cloud environments, applications, network devices — anything generating events feeds into the SIEM. It aggregates all of that data into a single place, applies correlation rules to find patterns that look like threats, and fires alerts when those patterns are detected.
This is genuinely valuable. Without a SIEM, a security team is looking at the world through multiple separate windows, each showing a partial view. A login from an unusual location, a large file transfer, a spike in outbound traffic — individually, each is a data point. Correlated together, they are an incident. SIEM does the correlation.
Where SIEM stops is important to understand. It detects and it alerts. It does not act. When a SIEM fires an alert, a human — or another system — has to decide what to do with it. The alert goes into a queue. An analyst picks it up, investigates, determines whether it is real or a false positive, and figures out the appropriate response.
At low alert volumes, that model works. At the alert volumes modern enterprises actually generate, it breaks. The average enterprise SOC receives somewhere between one thousand and five thousand alerts per day. Studies consistently show that seventy to ninety-five percent of those alerts are false positives. SIEM generates all of them. It does not prioritise them. It does not investigate them. It does not close them. It fires them into the queue and waits.
| SIEM tells you something happened. What happens next is still your problem. |
There is a second limitation worth naming. SIEM requires significant tuning to remain accurate. The correlation rules that generate alerts need to be maintained, adjusted as the environment changes, and updated as new threats emerge. In most organisations, this tuning work consumes a meaningful portion of engineering time — time that is not being spent on actual threats.
None of this makes SIEM wrong or outdated. It makes SIEM the detection layer — the foundation. The problem is when organisations treat the detection layer as the whole structure.
What SOAR Does — and Where It Fits
Security Orchestration, Automation and Response. SOAR came into the industry as a direct response to the problem SIEM created: the alert that fires and waits.
SOAR takes those alerts — from SIEM, from EDR, from threat intelligence feeds, from cloud monitoring tools, from anywhere — and does something with them. It investigates. It enriches the alert with context from threat intelligence sources, from asset databases, from identity systems. It runs automated workflows — playbooks — that handle the routine work of an investigation without requiring a human to do it manually.
In practice, this means that a phishing alert that would previously arrive in an analyst’s queue and wait for them to manually look up the sender domain, check the URL against threat intel, pull the affected user’s recent activity, and assess the risk — can now be handled automatically. The SOAR platform does all of that, produces a risk assessment, and either closes the case (if it is clearly benign), escalates it with full context (if it is genuinely suspicious), or executes a containment action (if it is confirmed malicious).
The measurable difference is response time. Organisations that implement SOAR consistently report significant reductions in mean time to respond — from hours to minutes for the types of incidents that automation handles well. This is not theoretical. It is the primary reason the category exists.
| SOAR does not make your analysts redundant. It makes them stop doing the work that was never a good use of their expertise in the first place. |
SOAR also changes what analysts spend their time on. Instead of triaging hundreds of low-confidence alerts to find the five that are real, analysts focus on the five that actually need human judgement. Threat hunting. Complex investigations. Incidents that do not fit pre-defined patterns. The high-value work that gets consistently deprioritised when the queue is infinite.
The playbook question
Most conversations about SOAR eventually reach playbooks — the automated workflows that define what the system does when a specific type of alert fires.
Traditional SOAR required security engineers to write these playbooks manually. A playbook for phishing. A playbook for ransomware. A playbook for credential stuffing. Each one a defined sequence of steps that the system follows. This was better than nothing, but it had a structural limitation: playbooks only exist for threat types somebody thought to write a playbook for. Novel threats, unfamiliar attack patterns, incidents that do not match a pre-built template — those still land in the analyst queue, still require manual investigation, still create bottlenecks.
Newer generations of security automation platforms address this by using AI to reason about unfamiliar alerts rather than requiring a pre-written response for every possible scenario. This is a meaningful evolution from the original SOAR model, and it is worth understanding when evaluating modern platforms.
The Key Differences — Side by Side
| SIEM | SOAR | |
| Primary job | Collect, correlate and alert on security events | Investigate, orchestrate and respond to security events |
| Core function | Detection and visibility | Automation and action |
| What it does well | Log aggregation, compliance reporting, anomaly detection across infrastructure | Reducing manual triage, running playbooks, integrating tools, managing cases |
| Where it falls short | Generates alerts — does not act on them. High false positive rates without serious tuning. | Needs a data source feeding it alerts. Cannot detect what it has not been told to look for. |
| Output | Alerts and dashboards | Closed cases, automated actions, investigation reports |
| Without the other | Alert queue that grows faster than analysts can work through it | Fast responses to incidents it may never discover on its own |
| Together | SIEM feeds alerts into SOAR — SOAR decides what to do with them | The foundation of a functioning modern SOC |
Do You Actually Need Both?
This is the question most organisations are actually trying to answer when they search for ‘SOAR vs SIEM.’ The honest answer is: in almost every case, yes.
Here is why the question is framed wrongly in most comparisons. SIEM and SOAR are not alternatives. They are sequential. SIEM generates the alerts. SOAR acts on them. Running SOAR without a SIEM means running automated responses against an incomplete picture of your environment. Running SIEM without SOAR means having a detection system that creates more work than your analysts can realistically handle.
The organisations that get the most value from their security operations infrastructure have both working together: SIEM as the detection layer that sees everything, SOAR as the response layer that decides what to do with what SIEM sees.
| If your SOC does not have a SOAR solution, odds are it is not a mature operation — regardless of how good the SIEM is. |
When SIEM alone is insufficient
A SIEM with no automation layer creates a specific failure mode. Alerts accumulate. The queue grows. Analysts work through the queue sequentially, starting with the most recent or the highest-severity flagged items. Older alerts age out — not because they have been investigated, but because nobody got to them. Real incidents sit in the queue for hours or days, not because they were missed by detection, but because there was not enough human capacity to action them.
This is alert fatigue. It is not a technology problem. It is a capacity problem that technology should solve — and SIEM alone does not solve it.
When SOAR without SIEM has gaps
SOAR platforms can ingest alerts from multiple sources and do not strictly require a SIEM. But an organisation that has SOAR without SIEM typically has significant blind spots in detection. SOAR responds to alerts it receives. If it is not receiving alerts from a comprehensive, correlated view of the environment, it is automating responses to an incomplete picture.
Cloud infrastructure, legacy on-premises systems, network traffic anomalies that only become visible when correlated across data sources — these are the things SIEM is built to surface. Without it, SOAR is automating well but potentially missing the signals that indicate the most serious threats.
The practical question to ask
Rather than ‘do we need both,’ the more useful question is: where in our current security operations does the process break down?
If alerts are being generated and the team cannot work through them fast enough — the gap is in response automation. SOAR addresses that.
If the team is not confident they are seeing everything happening in the environment, or if correlation across data sources is weak — the gap is in detection and visibility. SIEM addresses that.
Most mature security teams will find that both gaps exist. The order in which to address them depends on which one is creating more risk right now.
What to Look for When Evaluating Each
Evaluating a SIEM
The core questions are about coverage and accuracy. Does it ingest from every data source in your environment — including cloud? How sophisticated are the correlation rules? How much tuning work is required to keep false positive rates manageable? Does it support compliance reporting for the frameworks your organisation must satisfy? How does it handle data retention and forensic investigation?
A secondary question that many teams underweight: what does the SIEM hand off to when it fires an alert? If the answer is ‘a human analyst with no automated support,’ the SIEM is only solving half the problem.
Evaluating a SOAR platform
The primary questions are about what happens to an alert once SOAR receives it. What integrations does it support — and how many of your current security tools are covered? How are playbooks built — does it require engineering resources to write and maintain them, or does the platform offer more intelligent automation that handles novel scenarios? What does the investigation output look like — can an analyst understand why the system made the decision it made?
That last question is increasingly important. SOAR platforms that produce automated verdicts without visible reasoning create a new problem: analysts who cannot verify the AI’s logic cannot calibrate their trust in it, and organisations cannot produce audit-ready documentation of their automated security decisions. Explainability is not a luxury feature — in regulated industries, it is becoming a compliance requirement.
A practical test: ask any SOAR vendor to walk you through a real alert from ingestion to verdict. Watch how much of the reasoning is visible. If the platform produces a result but cannot show its work, that is a meaningful limitation.
A Note on XDR
Increasingly, conversations about SIEM and SOAR also include XDR — Extended Detection and Response. XDR combines detection and response into a single platform, typically built around an endpoint and cloud security stack.
XDR is genuinely useful in environments that are heavily consolidated around a single vendor ecosystem. It can reduce tool sprawl and provide good detection and response capability within its native stack.
Where it has limitations: XDR does not replace SIEM’s log aggregation and compliance capabilities, and it does not have the orchestration depth of a mature SOAR platform when it comes to integrating with a diverse security toolset. For organisations running multi-vendor environments or with strict compliance and audit requirements, XDR typically complements rather than replaces both SIEM and SOAR.
The short version: XDR is worth evaluating, but it is not the answer to ‘should I have SIEM and SOAR.’ It is a separate question.
Summary
SIEM and SOAR do different jobs. SIEM detects. SOAR responds. They are most effective when used together, with SIEM providing the comprehensive view of the environment and SOAR providing the automated capability to act on what SIEM surfaces.
Choosing between them is the wrong frame. The right frame is: which capability gap creates the most risk in your current security operations, and which one do you close first?
For most organisations, the answer to ‘do we need both’ is yes — but arriving at that answer on your own terms, with a clear understanding of what each one does, is more useful than any vendor telling you what you need.
Frequently Asked Questions
What is the main difference between SIEM and SOAR?
SIEM collects and analyses security data from across your environment to detect threats and generate alerts. SOAR takes those alerts and automates the investigation and response — running playbooks, enriching cases with threat intelligence, and either closing cases automatically or escalating them to analysts with full context. SIEM detects. SOAR responds. They are designed to work together, not replace each other.
Can SOAR replace SIEM?
No. SOAR needs a source of alerts to act on. Without SIEM’s comprehensive view of the environment, SOAR will be automating responses to an incomplete picture. SIEM provides the detection layer. SOAR provides the response layer. Removing either one creates significant gaps in security operations.
Can SIEM replace SOAR?
SIEM cannot automate investigation or response — it can only generate alerts. Organisations that run SIEM without SOAR typically end up with more alerts than their analyst team can work through, leading to alert fatigue, missed incidents, and very slow response times. SIEM is necessary but not sufficient for a mature security operations function.
What is the difference between SOAR and XDR?
SOAR is designed to orchestrate and automate security operations across a wide range of integrated tools — it is tool-agnostic and built for complex, multi-vendor environments. XDR combines detection and response in a single platform, typically built around a specific vendor’s security stack. XDR works well in consolidated environments. SOAR is more appropriate when you have a diverse security toolset and need orchestration across all of it.
How does SOAR reduce alert fatigue?
SOAR reduces alert fatigue by automating the investigation and triage of incoming alerts — enriching each one with threat intelligence, running playbooks to determine whether it is a genuine threat, and closing false positives automatically. Instead of every alert requiring a human analyst to manually investigate, only the alerts that are confirmed threats or genuinely ambiguous cases reach the analyst queue. This significantly reduces the volume of alerts analysts must work through manually.